As the world goes full steam ahead toward a digital economy, both the private and public sectors are looking to bolster their online capabilities across the board, and especially through digital identity verification. A new study from Juniper Research has found that spending on digital identity verification by businesses will reach $16.7 billion in 2026, […]
Cybersecurity
If your business falls victim to ransomware and you want simple advice on whether to pay the criminals, don’t expect much help from the U.S. government. The answer is apt to be: It depends. “It is the position of the U.S. government that we strongly discourage the payment of ransoms,” Eric Goldstein, a top cybersecurity […]
As ransomware attacks surge, the FBI is doubling down on its guidance to affected businesses: Don’t pay the cybercriminals. But the U.S. government also offers a little-noticed incentive for those who do pay: The ransoms may be tax deductible. The IRS offers no formal guidance on ransomware payments, but multiple tax experts interviewed by The […]
Carnival Corp. said Thursday that a data breach in March might have exposed personal information about customers and employees on Carnival Cruise Line, Holland America Line and Princess Cruises. In a letter to customers, the company indicated that outsiders might have gained access to Social Security numbers, passport numbers, dates of birth, addresses and health […]
NortonLifeLock, a global leader in consumer Cyber Safety, announced on Monday new and expanded privacy offerings to help people keep their sensitive information more private and take control of the information shared about them online. More than half of consumers globally don’t know how to protect their online privacy, leaving many defenseless to cybercriminals, according […]
Security today announced the results of a global survey examining consumers’ digital behaviors during the pandemic, as well as their potential long-term impact on cybersecurity. With society becoming increasingly accustomed to digital-first interactions, the study found that preferences for convenience often outweighed security and privacy concerns among individuals surveyed – leading to poor choices around […]
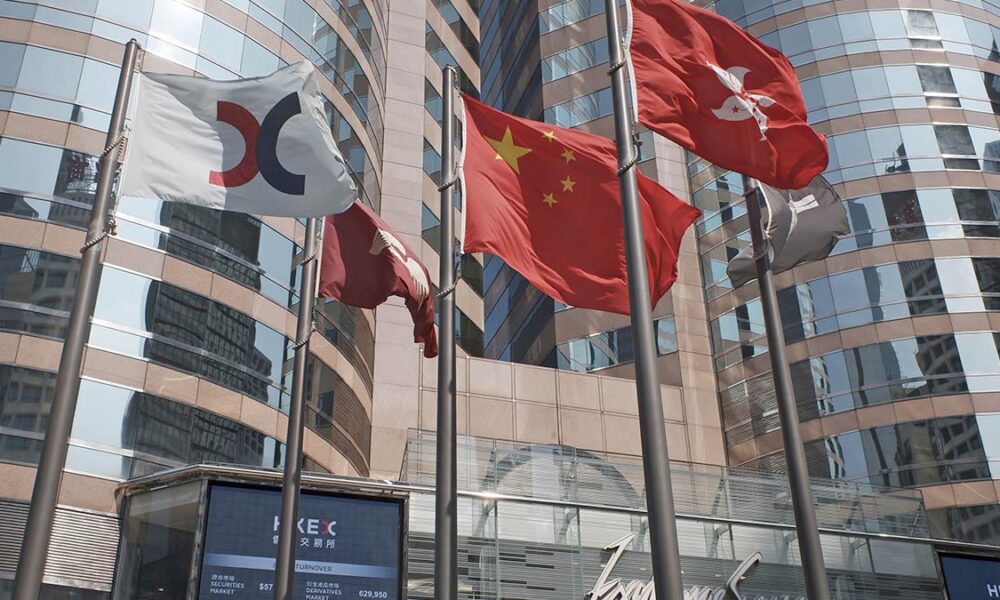
A software bug at a major network provider briefly knocked dozens of financial institutions, airlines and other companies across the globe offline during peak business hours in Asia. Akamai, which runs one of the internet’s main content-delivery systems, said the outage Thursday was not caused by a cyberattack, but rather a software bug on a […]
Cyber security is a fascinating, challenging, and vigorous profession, not for the complacent nor the faint hearted. Every employer wants to hire the best candidates with the most potential to become even greater and evolve alongside this young and tumultuous craft. Here are five essential qualities that every cyber security professional should strive to cultivate, and that employers should keep an […]
A cyberespionage campaign blamed on China was more sweeping than previously known, with suspected state-backed hackers exploiting a device meant to boost internet security to penetrate the computers of critical U.S. entities. The hack of Pulse Connect Secure networking devices came to light in April, but its scope is only now starting to become clear. […]
McDonald’s has become the latest company to be hit by a data breach after unauthorized activity on its network exposed the personal data of some customers in South Korea and Taiwan. McDonald’s Corp. said Friday that it quickly identified and contained the incident and that a thorough investigation was done. “While we were able to […]