Over the past three years, telecom tech and cellular infrastructure have been weaponized by Israel to track thousands of citizens across more than ten countries, according to Haaretz and Citizen Lab.
Commercial surveillance vendors have exploited the infrastructure of the global telecommunications networks by morphing ordinary cellphones into covert tracking beacons, without the knowledge – or consent – of their carriers, governments, and even their owners.
Since November 2022, researchers identified more than 15,700 discrete tracking attempts, routed through Israeli-based mobile network operators (MNOs), including 019 Mobile and Partner Communications.
As for the targets, well, in typical Israeli ‘target on your back’ behavior, they ranged from diplomats, journalists, and activists from more than ten countries, with Thailand, Norway, South Africa, and Bangladesh among the countries on the list.
The infrastructure targeted by the Israeli entities were “ranging from legacy networks built in the 1970s to the latest 5G systems has been repurposed into surveillance tools.” Basically, since 2022 Israel successfully created a mercenary market that flourishes within the very structure of the global mobile network system.
The Israeli targeting of telecoms tech followed one mechanism that’s dominantly centered around Signaling System No. 7 (SS7) and its successor, Diameter protocols designed for roaming that have been effectively hijacked for real-time geolocation.
SS7 is a signaling protocol that was developed back in 1975 that undergirds the routing of calls, texts, and location data across virtually every mobile network on Earth. SS7’s vulnerability has been documented in academic research and congressional testimony for more than a decade.
Just last week, British regulators banned unauthorized mobile tracking, transforming such legacy telecom tech protocols into a regulated security frontier to protect citizens from systemic state sponsored surveillance, according to the report by Citizen Lab.
The Israeli telecom network infrastructure that was used to track citizens had turned each and every country’s very same telecom network infrastructure into sophisticated espionage weapon.
By exploiting these “insecure by design” telecom tech systems, surveillance companies bypass modern encryption to pinpoint a user’s location with surgical precision.
Swiss ‘Neutrality’ Doesn’t Apply to Fink Telecom
Since 2023, a nexus between a Swiss telecommunication and Israeli surveillance has intensified, revealing a bridge between Alpine infrastructure and Israel’s intelligence presence and infiltration.
According to Haaretz and Citizen Lab, Switzerland’s “Fink Telecom Services” has reportedly allowed Israeli surveillance companies, such as Rayzone Group and Israeli-American company Cognyte, to “impersonate cellular carriers and connect to legacy mobile networks.”
By leasing technical identifiers known as “Global Titles,” this collaboration allows these companies to “launder” their tracking requests through a neutral European hub, effectively masking their origin and bypassing the security filters of foreign operators.
The observed telecoms tech partnership between Switzerland’s Fink and Israel’s Rayzone Group sits in direct contradiction with Switzerland’s legal evolution, and its overall “neutrality” stance on geopolitical matters and interferences.
In September 2023, the new Federal Act on Data Protection (nFADP) came into force, explicitly introducing “Privacy by Design” and requiring that “default settings must offer the highest level of data protection.” However, the exploitation of Swiss infrastructure for global “zero-click” tracking suggests a systemic loophole.
While the nFADP protects the privacy of those living in Switzerland, it appears ill equipped to prevent domestic telecoms tech from acting as “Ghost Operators” for international infiltrations, effectively allowing infrastructure to remain technically compliant while undermining the spirit of Swiss privacy neutrality.
Both Rayzone and Cognyte’s operational architecture behind the tracking campaign was, by design, built to be invisible. There was no way around that.
According to the Haaretz, both companies routed their surveillance operations through the intermediary Swiss registered, Fink, by extension making the Swiss entity as middleman that functioned as a ghost carrier.
Switzerland’s Fink, in its turn, impersonated legitimate cellular operators to inject malicious commands directly into the global signaling ecosystem. The structure created by Find, alongside the Israeli’s partners in crime, is what made the structure legally useful as it was technically effective.
Rayzone and Cognyte’s plan was facilitated by Fink as it interposed as a nominally independent European company between the suveillance vendor and the attack traffic. The arrangement diffused attribution across multiple jurisdictions, each with its own regulatory framework and none with clear oversight of the whole espionage operation.
SkyLock and the SS7 Vulnerability Loop
The tactical execution of these global “pings” often points toward the Israeli American company Cognyte and its specialized software, SkyLock. Originally a division of Verint, Cognyte’s platform exploits the SS7 protocol by sending “stealth” messages that are invisible to the target but force the SIM card to reveal the device’s location.
Internal documents “revealed that Verint, the parent company of Cognyte, sold an SS7-based location tracking system called SkyLock to a government client in the Democratic Republic of Congo,” highlighting the export of these tools to regimes with fraught human rights records.
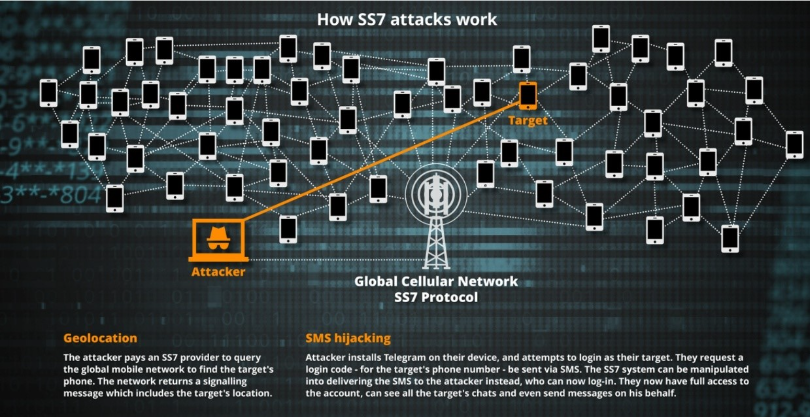
In layman terms, and simply put, the SS7 attack mechanics are nothing but a blatant trust violation in telecom tech. The protocol was built on a legacy “inter-operator trust model,” so it lacks modern authentication, allowing companies to conduct thousands of queries across countries, such as Norway and Thailand.
Presently, Cognyte continues to secure multi-million-dollar contracts for its “investigative analytics.” As for the industry, it will probably face a reckoning if the same telecom technology services used to route an international call is now being used to facilitate what researchers describe as the transformation of cellular carriers into “global tracking devices.”
The convergence of Israeli telecom tech surveillance sophistication with Swiss network access marks a definitive end to the phase of digital sovereignty, proving that as long as the world’s cellular networks remain interconnected, a “neutral” border is no barrier to a silent, state sponsored ring.
Israeli Expansionist Plans of Perpetual Surveillance
As of time of writing, Israel is actively seizing land in the West Bank, Gaza, and Southern Lebanon – a sovereign country neighboring the Jewish state’s North borders. Israeli expansionist plans are not just limited to geographical takeover of land, but its government and IDF’s enforcement of high-tech monitoring system over Palestinians and Lebanese citizens to guarantee Israeli control.
Israels neighboring country, Lebanon, became a testing ground for cell phone network infrastructure infiltration through means involving AI, facial recognition, and biometric data to create panopticon environment, according to Anadolu.
The systemic reach of these vulnerabilities is most visible in Lebanon, where Israeli intelligence has gathered data on citizens for years through extensive telecom infrastructure data infiltration. By gaining real-time access to data on Lebanese civilians, the Israeli Defense Forces (IDF) has effectively turned the nation’s telecom backbone into a tool for Psychological Operations (PSYOPS) campaigns conducted to destabilize local communities.
This has led Israel to send targeted “warnings” to specific individuals from domestic numbers, urging evacuations while simultaneously tracking both Lebanese citizens and visitors through sophisticated spyware on mobile phone network infrastructure, in some cases, before assassinating them.
This aggressive move is not a new one, as Israel maintains a cemented principle of tactical global telecom and technology infiltrations to “protect” its interests.
Can international rules and regulations ever truly protect nations from an intelligence tackle that views borderless digital infiltration on telecom tech as a sovereign right, same way Israel is doing? Or will international organizations turning a blind eye on Israel’s surveillance acts make such act permissible for all nations?
Inside Telecom provides you with an extensive list of content covering all aspects of the tech industry. Keep an eye on our Telecom sections to stay informed and up-to-date with our daily articles.