By now, it is commonly known that scammers have excelled in the art of evading recognition and being discovered. Yet one technology seems to be the match for such fraudsters as they unleash the wrath of sophisticated, complicated cyber attacks with the never-ending development of elaborate strategies to manipulate systematic strategies. The implementation of behavioral biometrics in identifying these scammers’ digital identities is an additional security layer that guarantees other security measures to further defend from any potential risky decisions that could hold heavy repercussions.
What is Biometric Digital Identity?
While some may not be fully aware of this, at this moment, as you are reading this sentence, as you are scrolling this article, as you use your smartphones, laptop, tab – or whatever preferable means to read this content – the idea of what the future might look like is already here. By future, I don’t mean flying cars and invading aliens with superior intelligence or such things. It’s the future of technological development, from Artificial Intelligence (AI) image generation, brain reading robots, 3D printed bones, and realistic holographs, to rapidly developing biometric technologies such as multi-factor biometrics identity and authentication and behavioral biometric authentication and identity.
With the embrace of digital transformation on all fronts, the world’s reliance on technological means to identify people demands a more advanced approach the ensure reliable results. From there comes the importance of integrating physiological biometrics features in digital identity to further optimize security processes and guarantee the lowest rate of fraud threats on users from any companies counting on any form of digital techniques.
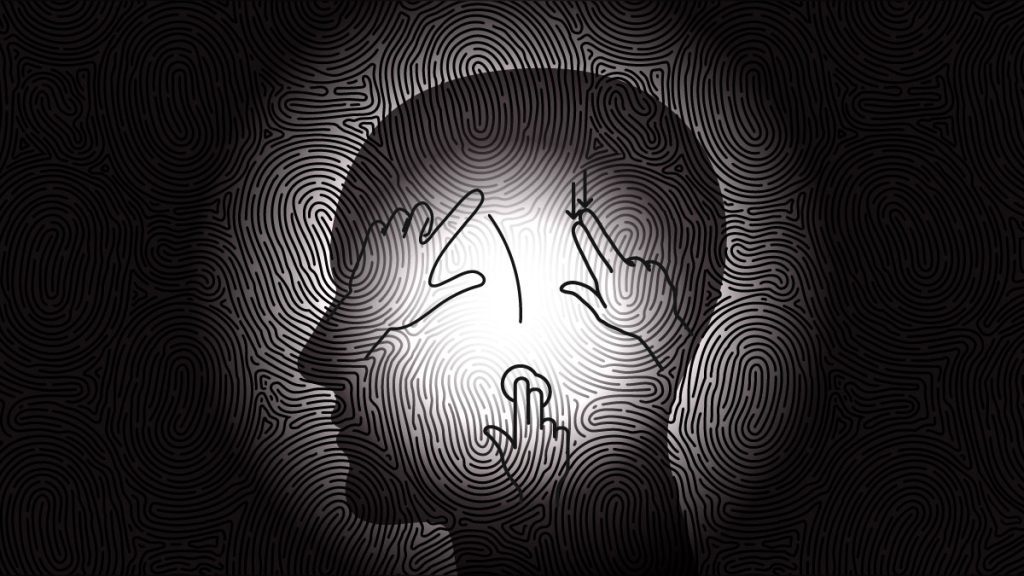
Digital identity for any establishment solemnly relies on intensifying the management of customers’ and users’ identities with a more protected approach. Facial recognition, fingerprint readings, and state-of-the-art advanced biometrics algorithms will increase security measures and protection for any establishment or company. With the ever-increasing need to ensure the safety of any identity, biometrics’ popularity is on an exponential rise as a means to identify people, whether online or offline.
Taking into account that a digital identity is the same as physical ID documents – except in a digital form, of course – its primary purpose is the online digital identity verification of individuals with a more secure approach. The goal is to counteract any opportunity of impersonality and forging documents – all while protecting the individual’s privacy and personal information. While the types of biometrical biometrics for digital identities are increasing, the most commonly adopted ones are facial recognition, voice recognition, and fingerprint scans.
What is Behavioral Biometrics Method?
When we talk about behavioral biometrics application for authentication purposes, we mainly mean harnessing any behavior related to an individual’s behavior to identify their identity to initiate access to digital services.
Continuous authentication using behavioral biometrics delivers an additional layer of security compared to numerous other authentication solutions, solely relying on the status information. As fraud and account theft increase, the need for implementing behavioral biometrics digital identity solutions has never been higher. The adoption of authentication methods using biometrics data has proven to be a necessity for establishing more than an additional luxurious layer of protection.
While the scope of a behavioral biometrics solution is continuously progressing, three main types of behavioral biometrics have maintained their position as the leading digital identity verification methods.
Device-Based Gestures
- Keystroke Dynamics are typing patterns that are different by nature from one person to another. These dynamics involve the combination of speed in typing and duration.
- Cursor Movements refer to some of the unique variations that the usual patterns in a mouse or trackpad cursor movement. This means paths, tracking speed, alteration in direction, clicks, and any type of association between the previously mentioned.
Body Movement and Voice Inputs
- Posture is one the most unique features of a human and how they conduct and present themselves. Body posture is one of the leading behavioral biometrics authentication features that enhance the experience, as well as fundamentally identify each person from the other. Recognizing biometric features through body postures ranges from the posture when performing basic swipes on any smartphone to identifying the swipe movement and its relation to the specific posture when being positioned in a particular manner.
- Voice ID is very different than commonly known voice recognition technology as it does not dissect the voice. Still, it is more lenient towards the characteristics of how the individual communicates. This means frequent pauses in a sentence, rhythms, pitch variations, and other elements that differentiate one person from another.
Inside Telecom provides you with an extensive list of content covering all aspects of the tech industry. Keep an eye on our Technology sections to stay informed and up-to-date with our daily articles.
