
Google, device manufacturers, and third-party apps could be probing deeper into users’ on-device habits by creating a tailing road to survey their every interaction through Android’s apps OS, a Trinity College’s study revealed.
Data breaches and password leaks have taken the world by a swoop the minute a global conceptualization broke out that no one is safe. Some of the most prominent names in the tech industry found themselves heavily exposed to some of the most memorable data breaches since the emergence of the digital era, such as Facebook, Microsoft, Yahoo, and of course, Google, with its 2018 data breach.
Now, digital privacy has presented itself as a fundamental element to safeguard companies, governmental agencies, and even users from any malicious attack that could fall upon any establishment’s “secure” infrastructure to reach our personal accounts.
For those who have a preferential turn towards Android phones and are worried about their privacy – as they should be – you probably covered the basic steps to maintain the defensive barrier against any security violation on any device.
The decision of securing your devices is rightfully yours, this aspect is undeniable, but what if all the extra measures you are taking to shield your devices are not enough? What if all those steps still cannot prevent any future hack?
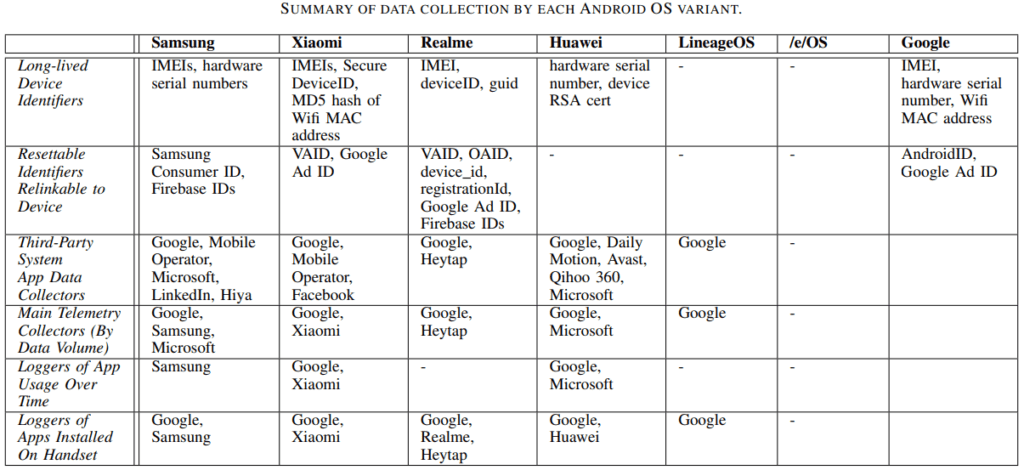
Dublin’s Trinity College researchers published a paper elaborating how Android mobile OS, specifically devices created by Samsung, Xiaomi, Huawei, and Realme, transmit a significant volume of information to the OS developer and third-party platforms. Some of these platforms are Google, Microsoft, LinkedIn, Facebook, and many more.
It goes without saying that at heart, users always knew their devices were not safe from outside digital privacy violation, but what does it mean coming from the manufacturers and the OS developers themselves? Particularly if we perceive this from an aspect that the Big Tech companies have been promoting their “safeguarding users’ privacy” ideology when in reality, they too have a hand in breaching their own digital privacy rules?
“The analysis of whether mobile apps disclosed sensitive information to their associated back-end servers has been the focus of much research, especially with the view of risks such as user de-anonymization, location tracking, behavior profiling, and cross-linking of data by different stakeholders in the device/software supply chain,” the paper revealed.
The most acute part of this scenario is that even if users were willing to opt-out, they can’t. The approach is embedded into the core of their device’s software, users have no option, or a choice for that matter, of reconfiguring its settings.
Most of the liability falls on what is known as “system apps” that come pre-installed into the system by the hardware manufacturer to provide a number of services, such as camera or messaging apps. These services are referred to as “read-only memory” (ROM) and are embedded into Android devices and cannot be deleted or modified.
Trinity’s research unveiled that these applications are endlessly sending the device’s data to the manufacturing company, which in return is sending the latter to more than one third-party app, even if users did not access the apps.
For example, when Microsoft and Samsung partnered up to branch Android and Windows together, this unity had more than meets the eye.
When Samsung devices come bundled up with Microsoft bloatware, packaged with the third-party app, LinkedIn, the hard-coded networking platform continuously relays to Microsoft servers detailed data about the device, such as unique identifiers and the amount of Microsoft apps installed on the user’s phone.
In parallel, the aggregated pinged data is sent to third-party analytics providers that the apps might intertwine with. Meaning, Google Analytics also has access to the device’s data, as this plug-in is a pre-installed system app embedded into the core Android software.
As for the hard-coded apps that demand advanced embedded credentials, often used on a day-to-day basis, send an exponentially larger mass of data revealing each interaction made on the platform, such as when and for how long users are using the app. These platforms share with Google Analytics certain specifics data with the search engine’s analytical branch.
The research paper single-handedly addressed a multitude of scenarios where these platforms are in direct breach of some undisclosed privacy breach.
Now, it is true that none of these data records can single out one device from a profusion of devices. However, when intertwined, they breed the ultimate “fingerprint” wielded to track any device, even if users opt-out.
In its defense, the search engine giant does include several “developer rules” aimed at thwarting certain invasive apps. These rules inform developers that they cannot connect a device’s special ad ID with a more tenacious element for any genre of ad-related function.
“I reset, a new advertising identifier must not be connected to a previous advertising identifier or data derived from a previous advertising identifier without the explicit consent of the user,” Google elaborated on the matter.
“You must abide by a user’s ‘Opt-out of Interest-based Advertising’ or ‘Opt-out of Ads Personalization setting. If a user has enabled this setting, you may not use the advertising identifier for creating user profiles for advertising purposes or for targeting users with personalized advertising,” the company added in its statement.
While these tracking features are embedded into the nucleus of Android devices, the question remains, what is the manufacturers’ role in this tracking framework? Is it simply to track the users’ movement, or is there a superior purpose that we are not familiar with?
Chances are, as regulators are continuously probing into these tech companies’ demeanor in breaching digital data privacy, this too might get exposed to a much more elevated scale of investigative regulatory behavior, if federal governmental figures recognized this issue as an identifiable form of data breach.
Inside Telecom provides you with an extensive list of content covering all aspects of the tech industry. Keep an eye on our Ethical Tech section to stay informed and up-to-date with our daily articles.